Attackers are continually devising new techniques to evade detection by security tools such as firewalls. Often, attackers start with an “exploit” to take advantage of a vulnerability within a firewall. But “evasions” are far worse. An attacker can use an evasion to disguise or manipulate malicious network traffic, enabling threats to slip past firewall defenses unnoticed. Evasions can involve altering packet structures, fragmenting data in unusual ways, or using encoding methods that standard firewall inspection processes cannot reliably detect.
In our recent Cloud Network Firewall (CNFW) test, we evaluated firewall effectiveness by assessing how well they recognize and counteract 2,500 attacks spanning 27 evasion techniques across multiple network layers. This provides a crucial measure of firewall robustness and overall security effectiveness.
For the CNFW test, CyberRatings integrates evasion scoring into a comprehensive security effectiveness metric through a detailed multiplier approach.
Security Effectiveness = Routing & Access Control × TLS/SSL Functionality × Exploits × Evasions × Stability & Reliability
Each component is scored on a scale from 0% to 100%. A low score, especially for evasions, significantly reduces the overall security effectiveness of the test.
How Firewall Evasion Impacts Your Security Posture in the CNFW Test
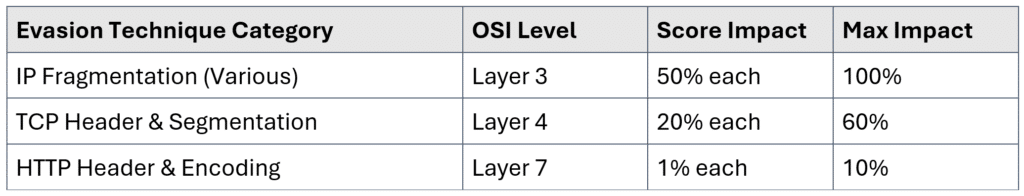
Our CNFW scoring starts at 100% and deducts points based on the firewall’s ability to detect evasions. Failing to detect lower-layer evasions, which are fundamental within the CNFW testing scenario, has the most significant impact.
OSI Layers and CNFW Test Impact
The OSI (Open Systems Interconnection) model provides a standardized framework for understanding data flow in network systems. Our CNFW test specifically evaluates evasion techniques across Layers 3, 4, and 7:
Layer 3 (Network Layer)
High Impact (50% per category, up to 100% total impact)
Layer 3 evasions, such as IP fragmentation and header manipulation, present the most significant risk in the CNFW test because they take place at the fundamental levels of network traffic inspection.
Common Layer 3 evasions:
- IP fragmentation: Data packets split to evade inspection.
- Header manipulation: Packet headers modified to bypass security.
Layer 4 (Transport Layer)
Moderate Impact (20% per category, up to 60% total impact)
In Layer 4, the CNFW test assesses evasions that manipulate packet sequencing or segmentation, challenging firewall connection monitoring.
Typical Layer 4 evasions:
- TCP segmentation: Packet fragmentation to disrupt monitoring.
- Sequence number manipulation: Confusing stateful inspection.
Layer 7 (Application Layer)
Lower Impact (1% per category, up to 10% total impact)
Layer 7 evasions within CNFW tests embed threats in typical web traffic, testing firewalls’ deep inspection abilities.
Examples of Layer 7 evasions:
- Manipulated HTTP headers: Concealed malicious requests.
- Chunked encoding: Traffic in misleading fragments.
CNFW Test Evasion Technique Scoring Breakdown
Linking CNFW Evasion Scores to Severity
The severity of evasion detection is particularly crucial in the context of our CNFW testing. An undetected evasion can create significant vulnerabilities, potentially allowing attackers unrestricted access. Therefore, firewalls that score poorly in evasion detection should be promptly reviewed, reconfigured, or replaced to maintain an optimal security posture against cyber threats.